Product Retirement
SP// WAF
StackPath is dedicating its entire focus to being the industry’s best cloud computing platform built at the internet’s edge. Subsequently, we are retiring the StackPath Web Application Firewall (SP// WAF) offering.
New SP// WAF subscriptions are no longer available, and SP// WAF and its add-on services/features will cease operations at 12:00 a.m. Central (UTC-6:00) on November 22, 2023.
Self-managed transition
SP// WAF users have full control over their account, subscriptions, and configurations through the SP// Customer Portal or API. Log in below to manage your transition or contact SP// Support for more information.
Learn more about StackPath
Platform
Our one-of-a-kind edge computing platform consists of strategically located facilities, a seamless global network, best-in-class operational and product automation and design, and enterprise-grade strength and scale.
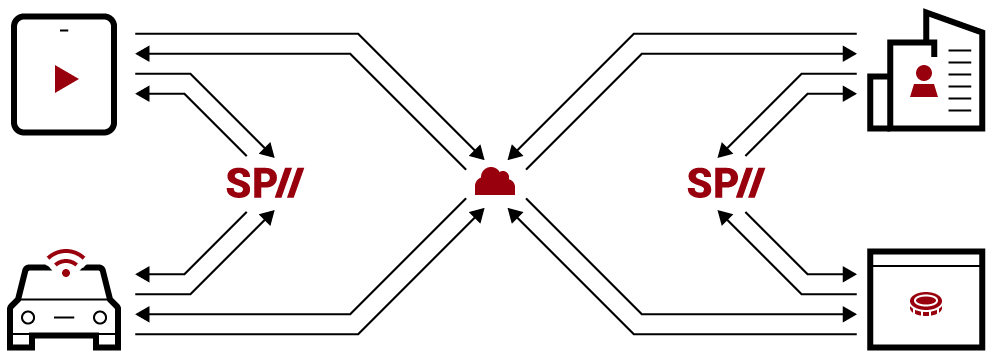
Edge compute
Provided at the edge of the internet, SP// Virtual Machines and Containers provide the distribution and proximity that latency-sensitive applications and real-time workloads need to perform and succeed.

