May 11 2023
Apr 18 2023
Resource
BlogTopic
Edge SecurityDate
Nov 15, 2022Enterprise applications and workloads are more heavily distributed than ever, residing in multiple private and public cloud environments. Meanwhile, users are also increasingly distributed and expect to consume applications from anywhere.
With access patterns today vastly different from how they were even five years ago, it is time to rethink how and where web applications should be protected from malicious exploits and abuses.
In the classic model depicted below, a Web Application Firewall (WAF) is placed co-adjacent to the application/s it protects.
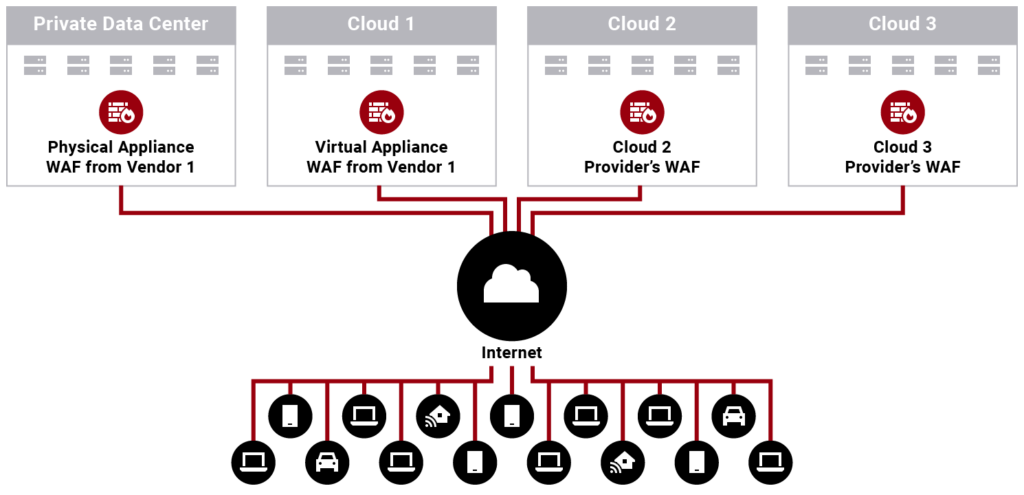
An enterprise typically has a legacy physical WAF appliance deployed in its private data centers. As the need arose to protect applications in centralized cloud platforms, the enterprise may have deployed in the cloud a virtual appliance from their physical WAF appliance vendor (as depicted in cloud 1) or a WAF service from the centralized cloud provider itself (as shown in cloud 2 and 3).
An appliance-based WAF—whether physical or virtual or deployed in a private or public cloud—has limitations:
A WAF service from a centralized cloud provider has limitations, too:
A multi-cloud world requires a different approach, as depicted below.
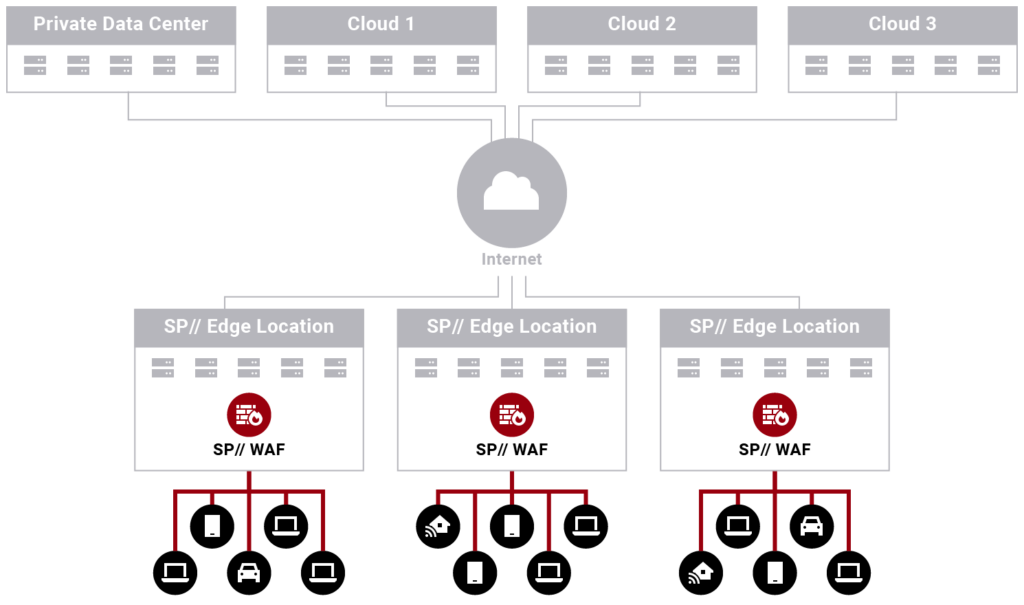
This model leverages a WAF service distributed across the internet’s edge in StackPath locations worldwide. Let’s refer to it as an edge WAF.
An edge WAF has the following benefits:
StackPath WAF offers all of the above benefits and is the way forward in a multi-cloud world. The StackPath WAF can be deployed in the following deployment models:
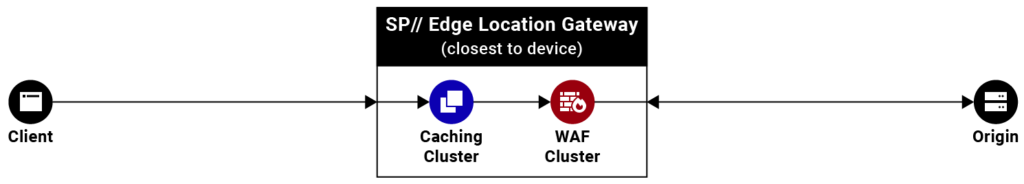
StackPath CDN + StackPath WAF
StackPath offers a CDN service in addition to WAF. An enterprise can leverage our CDN caching capabilities to cache static content while leveraging our WAF to protect origin calls.
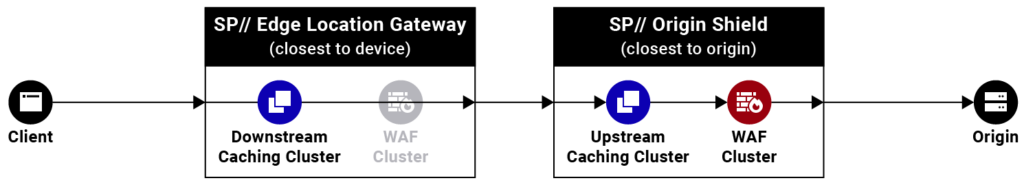
StackPath CDN + StackPath Origin Shield + StackPath WAF
A variation of Model 1, this deployment model takes advantage of Origin Shield to reduce the number of original calls that need to be made. A downstream caching cluster closest to the origin acts as an Origin Shield consolidating missed-cache requests from multiple upstream caching clusters closer to the users. The WAF sits between the Origin Shield and the origin.
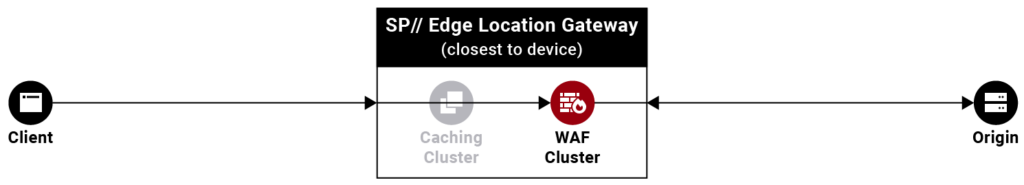
StackPath WAF Only
The StackPath edge cloud WAF can also be deployed standalone, not taking advantage of any caching capabilities. All user requests are policed and then sent to the origin.
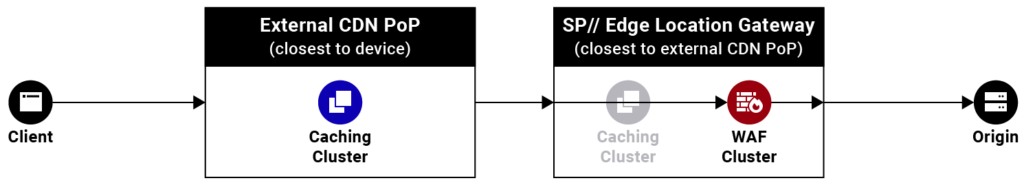
External CDN + StackPath WAF
We would love to have everyone use our CDN caching services, but in situations where that is not practical, the StackPath WAF can also sit between an external CDN and the origin.
We invite you to take advantage of the flexible deployment options of our cloud WAF to protect your web applications and APIs. For more information on our WAF Packages, check out our WAF page.